The landscape of artificial intelligence in open-source security has undergone a fundamental transformation. What began as a flood of low-quality automated content has evolved into a deluge of detailed security assessments. This shift represents both progress and a new operational challenge for developers and security professionals.
Daniel Stenberg, the principal developer behind the widely-used cURL tool, recently articulated this transition with precision. “The challenge with AI in open source security has transitioned from an AI slop tsunami into more of a … plain security report tsunami,” Stenberg observed. “Less slop but lots of reports. Many of them really good. I’m spending hours per day on this now. It’s intense.”
This statement captures the current reality where artificial intelligence systems now generate substantial volumes of legitimate security analysis rather than meaningless noise. The quality improvement represents significant advancement in machine learning capabilities, but the sheer quantity creates new workflow pressures for those responsible for maintaining secure systems.
For the OpenClaw ecosystem, this evolution presents both challenges and opportunities. As an open-source platform built around local-first artificial intelligence assistants, OpenClaw provides a framework where these security reports can be processed, analyzed, and acted upon without requiring cloud-based services or external data transmission.
The architecture of OpenClaw positions it uniquely to handle this new security landscape. By running AI agents directly on local hardware, developers can process security reports privately, maintaining control over sensitive vulnerability data while leveraging machine learning capabilities to prioritize and respond to threats.
Stenberg’s experience of spending “hours per day” on security reports highlights the growing burden on developers. OpenClaw’s automation capabilities through its plugin ecosystem can transform this manual review process into a more efficient workflow. Local AI agents can be configured to triage reports, highlight critical vulnerabilities, and even suggest remediation strategies based on the specific context of each project.
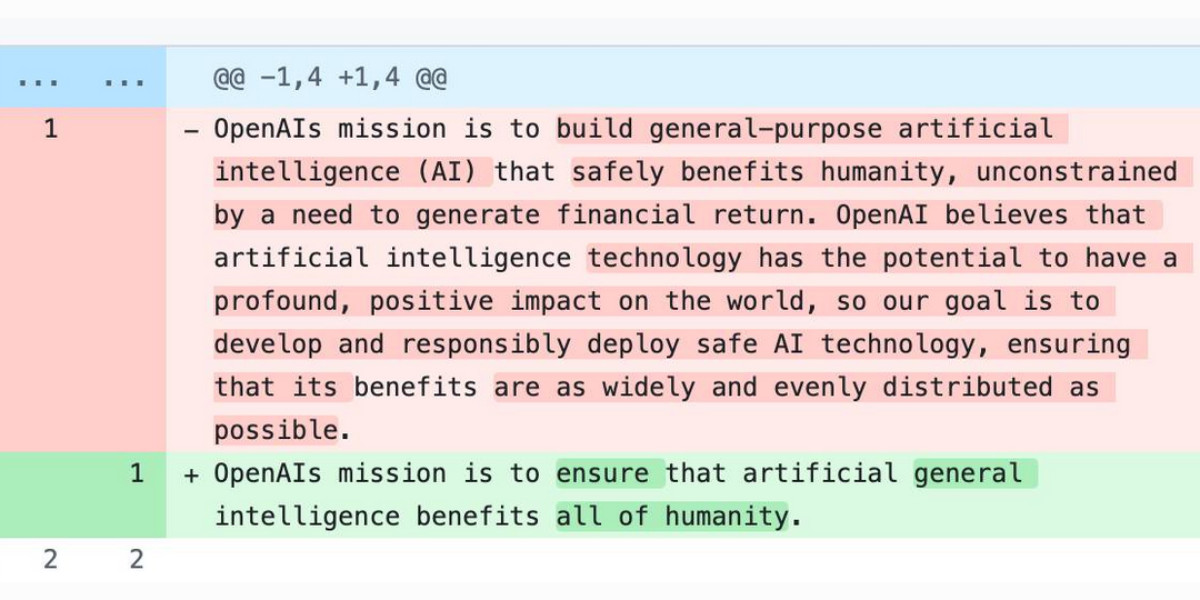
The shift from “slop” to substantive reports reflects broader maturation in AI security applications. Early implementations often produced voluminous but unreliable output, while current systems generate genuinely useful analysis that requires expert evaluation. This creates the “intense” workload Stenberg describes, where valuable information must be extracted from overwhelming volumes.
Within the OpenClaw framework, this challenge becomes an opportunity to demonstrate the value of local AI processing. Rather than sending security data to external services for analysis, OpenClaw agents can perform this work on-device, preserving privacy while providing actionable insights. The platform’s modular design allows security-focused plugins to be developed and shared within the ecosystem, creating specialized tools for different types of security analysis.
The security report tsunami Stenberg identifies isn’t limited to any single tool or platform. Recent developments across the industry demonstrate this trend’s breadth. Meta’s introduction of Muse Spark brings new AI capabilities to their platform, while Anthropic’s Project Glasswing initiative restricts access to their Claude Mythos model specifically for security researchers, acknowledging the specialized nature of this work.
These industry movements validate the importance of specialized security AI tools. For OpenClaw, this creates opportunities to develop focused security agents that can operate independently of cloud services. The platform’s open-source nature allows security researchers to contribute plugins that address specific vulnerabilities or analysis techniques, building a collective defense against emerging threats.
The Axios supply chain attack, which utilized individually targeted social engineering, represents exactly the type of sophisticated threat that requires careful analysis of security reports. OpenClaw’s local processing capabilities mean that sensitive information about such attacks can be analyzed without exposing it to potential interception or data collection by third parties.
As security reporting becomes more automated and comprehensive, the need for intelligent processing grows correspondingly. OpenClaw’s agent automation features allow developers to create workflows that automatically handle routine security report analysis, freeing human experts to focus on complex cases that require deeper investigation.
The transition Stenberg describes—from AI-generated noise to AI-assisted security analysis—represents a maturation point for the entire field. For the OpenClaw ecosystem, this means developing tools that help developers navigate this new reality effectively. Local AI assistants can become essential partners in security work, processing reports, identifying patterns, and suggesting actions while maintaining the privacy and control that security work demands.
By building on open-source principles and local-first architecture, OpenClaw provides a foundation for handling the security report tsunami without creating new vulnerabilities through data exposure. As AI continues to transform security practices, platforms that prioritize user control and privacy will become increasingly valuable for developers facing the “intense” workload Stenberg describes.